Table of contents
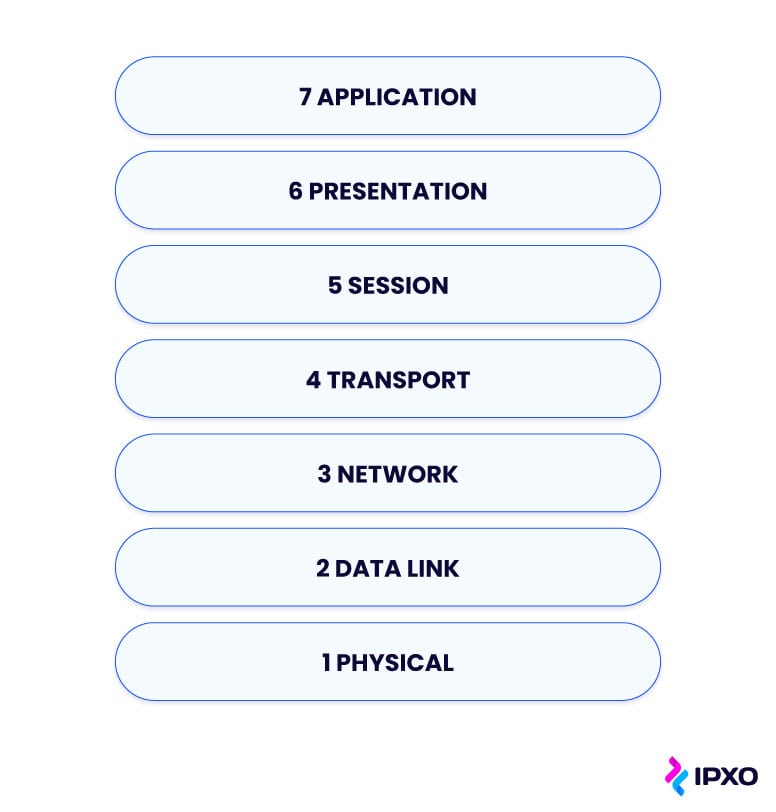
OSI Model In Networking Explained
Uncover the 7 OSI model layers and learn why it is important in networking.

About the author
Ignas is a Platform Engineering Manager at IPXO with more than 7 years of experience in the IT sector. His expertise includes network design solutions and infrastructure maintenance. After working hours, you will find Ignas in Lithuanian folk-dance classes.
Learn more about Ignas Anfalovas
Related reading

Managing IP Infrastructure at Scale: Challenges and Modern Solutions
One of the less-discussed yet highly relevant layers of managing modern internet infrastructure lies in IP infrastructure management. Even though it doesn’t get the same…
Read more
What Is a Network Source of Truth (NSoT) and Why It Matters for Modern IP Management
A reliable Network Source of Truth (NSoT) gives network teams full visibility and control by unifying IP data, automation, and compliance. Learn how IPXO helps organizations simplify network management…
Read more
Switching from AWS-Assigned IPs to BYOIP
Learn how to transition from AWS-assigned IPv4 addresses to your own Bring Your Own IP (BYOIP) ranges with minimal disruption.
Read moreSubscribe to the IPXO email and don’t miss any news!