Table of contents
How does a proxy server work?
Types of proxy servers
Should you use a proxy server?
Proxy risks
Conclusion
What Is a Proxy Server? A Beginner’s Guide
Learn what proxy is and how it can assist you by hiding your public IP address, improving speed and unlocking access to geo-blocked websites.

A proxy server, or simply a proxy, is a system you can use to access websites indirectly. In other words, instead of establishing a direct internet connection to web pages, you’re going through a proxy server that accesses them for you.
The proxy server acts as an intermediary server, so you don’t have to show your own IP address. This makes proxies similar to virtual private networks (VPNs). However, in this case, you do not establish a VPN tunnel for your internal network activity. Instead, a proxy server stands between your actual IP address and the websites you are visiting.
Many types of proxy servers exist, but they all have the same task – to represent you on the internet and conceal data while you’re surfing online.
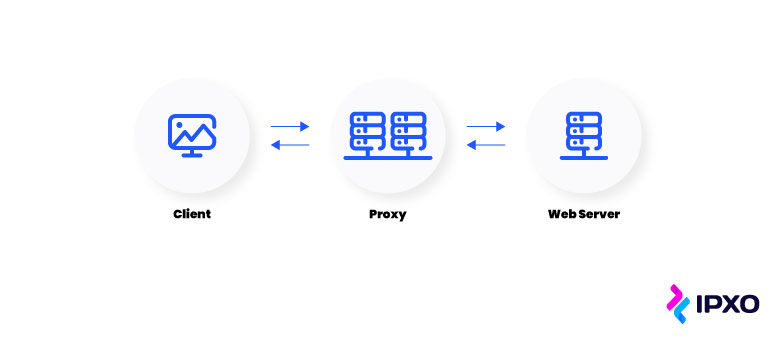
Here’s a step-by-step overview of what happens when using a web proxy:
- You send a web request when you try to access a website.
- The proxy server turns on, and the web request goes to it.
- Then, the proxy sends your web request to the relevant web server.
- The proxy receives a response and transfers the information to you.
- The web page loads.
At the end, you access the web page as per usual, but you and your IP address don’t have to establish a direct connection to that web page.
This beginner’s guide explains how proxy servers work and what their benefits are. Additionally, we discuss whether organizations and businesses need proxy servers and what risks they bring.
How does a proxy server work?
You already have the answer to the question of what a proxy is, but we still need to explain how this service works.
First of all, every computer connected to the internet has a unique Internet Protocol address (IP address). It represents your device’s address on the internet.
Every web proxy has its own IP address as well. That means that when you’re routing internet traffic via a web proxy server, you are effectively using that proxy’s IP address, not your device’s. Essentially, a proxy server masks your address while still sending the same results you would get if you were visiting web servers on your own.
In addition to that, a proxy web server can:
- Hide your location from the websites you’re visiting
- Encrypt your data so the destination server can’t read it
- Block access to specific websites based on their IP addresses
Setting up a proxy is easy, and you can usually do it on your internal network, browser, mobile device or computer. Naturally, the steps are different with different systems, but you usually use an automatic configuration script.
You can take the easy route by using proxy services from providers that usually charge a monthly fee. You can also use free proxy services, but paid options are still more suited and safe for businesses with many devices.
Now that we’ve covered that, let’s take a closer look at the main benefits of a proxy server.
Proxy server hides public IP address
The main feature of a proxy server is to hide your public IP address. For example, a typical forward proxy sits between you and external networks. It hides your IP address and uses its own. A forward proxy server does this by evaluating outbound web requests and taking specific actions before sending the request to you.
A proxy server can thus act as a firewall and web filter. It also enables you to hide your IP address and identity from websites and effectively allows you to surf the web anonymously. Due to that, websites cannot use the established internet connection to request information on your files, apps, personal information, data, etc.
It’s worth noting that proxy servers act as web filters against malicious activity by extension as they can also protect your device and data from hacking threats. This is especially important for businesses that want to prevent simple human errors from turning into massive data breaches. Of course, even with a proxy server at hand, you still need to take appropriate security measures.
Proxy server improves speed
Due to the unprecedented and exponential growth of the internet, the drain on its infrastructure has also grown. This has lead to:
- Network congestion
- Server overloading
- Speed issues for internet users
Proxy caching might help solve these issues.
Instead of obtaining the same information repeatedly, a proxy server stores the data in a cache and then sends it to the user. Because the cache is much closer to the user than the content they are trying to access, the speed at which they access it is improved.
In addition to that, with caching, web proxies can reduce network traffic to web servers and reduce network load. This is because the information no longer has to cross more of the network when stored in the cache of the caching proxies.
Proxy server caching is even more beneficial to organizations as it’s used more often. That’s because people within an organization likely have similar interests, which means they access the same websites and information. In turn, caches can store more relevant information, which further improves speed for everyone.
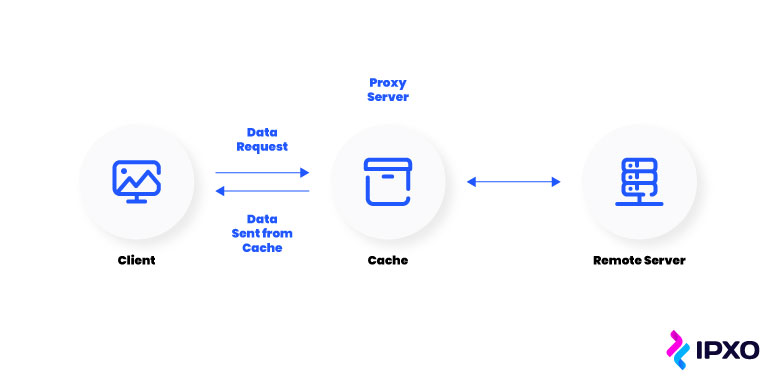
To sum up, proxy settings can do two important things: save bandwidth for the network and lower access latency for the client.
Proxy server allows accessing geo-blocked content
Many people don’t know exactly what geo-blocking is, but most have run into geo-blocked content.
In simple terms, geo-blocked content is every piece of content on the web that’s inaccessible to users from specific geographical locations. So, when you run into a video or an article with a message that this content is not available in your country – you’ve run into geo-blocked content.
In most cases, geo-blocking is used by companies and governments.
Companies
It is usually streaming services that have to abide by the terms of licensing deals and thus block access to specific content in specific countries. Of course, various other companies use geo-blocking as well.
Governments
In most cases, governments use geo-blocking to block entry to sites facilitating illegal activities. Most countries do this for any illegal activity they find.
In addition, geo-blocking is also used for reasons that many might find less legitimate:
- A government blocks popular websites it deems its citizens shouldn’t see
- An internet service provider saves bandwidth by throttling the internet
Geo-blocking is possible as it relies on tracking and geolocation services to identify an IP address and block it from accessing specific websites, depending on the IP geolocation. Organizations and governments do this en masse.
That said, because IP addresses are involved, it’s easy to bypass geo-blocking and access blocked content with the help of services that change or hide IP addresses. These services include:
- Proxy servers
- Virtual private networks (VPNs)
- Tor browsers
- Smart DNS or DNS changers
Proxy servers can bypass geo-blocking by accessing content for you. So, if your proxy server is located in a country that is not restricted, it won’t get blocked and, consequently, still send information to you even though you send the request from a restricted location.
Naturally, different types of proxies do this differently. For example, anonymous proxy servers use a simpler route by hiding your IP address. Organizations monitoring competitors or market trends often use web scraper APIs that manage proxy rotation automatically.
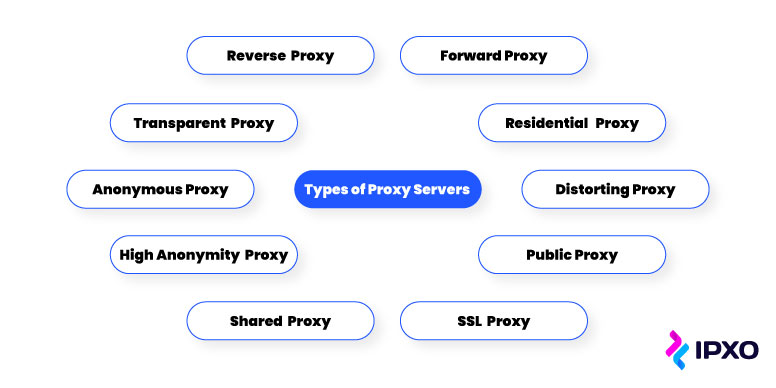
Types of proxy servers
Every proxy does the same thing – it gives you a different IP address. However, different types do this using different measures. The types of proxies you should know about are:
- Forward proxies
- Reverse proxies
- Transparent proxies
- Anonymous proxies
- High anonymity proxies
- Residential proxies
- Distorting proxies
- Public proxies
- Shared proxies
- SSL proxies
Forward proxies
A forward proxy server stands in front of users, and it’s primarily used in internal networks that want a single point of entry. It helps get data to larger groups in that internal network.
However, a forward proxy server can consequently limit the ability to serve individual clients effectively.
Reverse proxies
A reverse proxy server works by listening for connections on behalf of the server, not the client. Reverse proxy servers are effectively the opposite of forward proxies as they sit in front of the web servers, not the users.
They intercept web requests from users at the very edge of the web server and then send them toward and receive replies from the original server. This makes a reverse proxy perfect for organizations looking to reduce bandwidth load. However, they can still expose the server’s architecture if a hacker gets past the defenses.
Transparent proxies
A transparent proxy offers a regular browsing experience, and it does not modify requests or responses. It is also sometimes known as a forced proxy because it can easily be forced on users. For example, a company might use a transparent proxy to keep its employees unaware of the proxy’s existence.
The main disadvantage of transparent proxies is that they are less secure.
Anonymous proxies
An anonymous proxy keeps activity online untraceable. It effectively hides your personal information and the device’s information, but it has many limitations.
For example, public anonymous proxies offer no encryption, lack of full anonymity and low quality. Additionally, many view the use of anonymous proxies as a slightly dishonest behavior.
High anonymity proxies
A high anonymity proxy is an anonymous proxy taken to the next level. A high anonymity proxy erases your information before it connects to the website you’re trying to access.
However, it’s essential to know that only reputable high anonymity proxies are good while others are typically designed as traps.
Residential proxies
A residential proxy awards the user with an IP address of a specific device and then moves all requests through it. This makes them perfect for verifying ads as well as blocking unwanted ads and cookies.
Unfortunately, residential proxies also cost more money than most other types of proxies.
Distorting proxies
A distorting proxy works like many other proxies, but it also identifies itself as a proxy to keep its identity hidden. It does this by creating a fake IP address, and it’s perfect for market research, distorting location data and gaining high anonymity online.
The downside is that some sites tend to block these proxies automatically.
Public proxies
A public proxy is effectively a proxy server that doesn’t cost anything to use. Unsurprisingly, this often means that public proxies are less secure and effective than other types of proxies.
Shared proxies
A shared proxy is, well, a shared proxy. More than one user uses a shared proxy, and they are usually a good option for those not willing to spend a lot of money.
SSL proxies
An SSL proxy offers decryption between the server and the user. All data sent between the two is encrypted, so both parties can hide the proxy.
SSL proxies are great for organizations looking for better protection against threats that the Secure Socket Layer (SSL) protocol can reveal. The only downside is that these proxies cannot be cached.
Should you use a proxy server?
Proxy servers are not recommended to everyone. What’s more, alternatives like VPNs are often the more popular choice. That said, proxy servers still can be useful, especially for organizations and businesses.
Here are just some of the reasons why your business might choose to use a proxy server.
To save bandwidth and improve speed
We’ve already mentioned that organizations tend to gain better network performance with the help of caching proxy servers. When using proxies, there’s often no need to wait for incoming traffic to reach your internal networks when you can simply store information in caches and consequently improve bandwidth and speed.
To control how employees use the internet
By setting up a proxy server on the company network, you can effectively control and monitor what your employees see and do online. If you don’t want employees to waste time on sites they don’t need for work, you can deny them access through the proxy settings.
And if you’re unsure of how they’re using the web and whether they are using safe websites, you can employ the proxy server to monitor them and request them to change their behavior as needed.
To increase security and privacy
Hiding your IP address with a proxy can help protect you and improve your privacy online. You can also encrypt data and thus protect it from malicious prying eyes. Moreover, you can use the proxy server in conjunction with a VPN to make all requests from any external server go through the company proxy and enable better encryption.
Proxy risks
Unfortunately, besides the many advantages a proxy server can bring, there are some risks. The most common risks of using a proxy server are:
- Ineffectiveness
- No encryption
- Lack of privacy

Not all proxies are equally as effective. This is primarily true for free proxy services as their providers often do not invest enough in hardware and encryption. On top of that, some of these services are downright scams.
Furthermore, a proxy without proper encryption or no encryption at all can be very dangerous to use. Without encryption, the data is sent as plain text and, consequently, anyone can view it.
Moreover, many proxies keep your web requests saved locally without encrypting them. Due to this, your privacy can suffer. Therefore, it’s essential to check how the proxy server saves this data and what policies the service follows.
Conclusion
So, what is proxy? It’s an interesting solution for both individuals and organizations looking for more anonymity on the web. It effectively hides your address online, giving you more protection from prying eyes and also from malicious forces.
You can use various types of proxies for various purposes. You can even use them in conjunction with a virtual private network to improve your data’s encryption and, consequently, security.
Proxy servers are also perfect for businesses looking to gain more control, as they can help monitor how their employees use the internet and also help improve their data loss prevention measures.
About the author
Related reading

Managing IP Infrastructure at Scale: Challenges and Modern Solutions
One of the less-discussed yet highly relevant layers of managing modern internet infrastructure lies in IP infrastructure management. Even though it doesn’t get the same…
Read more
What Is a Network Source of Truth (NSoT) and Why It Matters for Modern IP Management
A reliable Network Source of Truth (NSoT) gives network teams full visibility and control by unifying IP data, automation, and compliance. Learn how IPXO helps organizations simplify network management…
Read more
Switching from AWS-Assigned IPs to BYOIP
Learn how to transition from AWS-assigned IPv4 addresses to your own Bring Your Own IP (BYOIP) ranges with minimal disruption.
Read moreSubscribe to the IPXO email and don’t miss any news!
