Home » Blog » IP Security
Table of contents
What are cyberthreats, and how prevalent are they today?
IP reputation scans
Prevention is key to successful IP address abuse mitigation
Cyberthreat Mitigation in the World of IPv4 Leasing
What is a cyberthreat? Why should it be mitigated? What are the best mitigation techniques? Keep reading to find answers and insights from the industry experts.
What is the first thing that comes to mind when you hear the words cyberthreat mitigation? Do you immediately remember that you have not changed your passwords in a while? Perhaps you think of two-factor authentication (2FA). Or you go back to an article you recently read about cyberespionage. What about IP address security?
Home internet users often have experience dealing with password breaches, hijacked accounts, ransomware invasion and other common types of cyberthreats. But did you know that your personal data is not the only thing at risk? IP addresses are also on target. This is a headache that mainly troubles internet services providers (ISPs), telecommunication companies and other IP holders that often manage thousands and millions of unique device identifiers.
Unfortunately, IP address abuse is prevalent, and it is likely to become even more common as Internet Protocol version 4 (IPv4) addresses are becoming scarcer and, at the same time, more desirable. In 2022, IPv4 addresses are treated as a commodity. That puts a target on the back of companies around the world that cannot afford to lose a crucial resource.
Although IP addresses can be affected by cybercriminals, threat mitigation techniques exist, and security experts continue enhancing them to ensure protection. Continue reading to learn more about cyberthreat mitigation in relation to IP addresses and IPv4 leasing.
What are cyberthreats, and how prevalent are they today?
A cyberthreat is a threat to the security of anyone using the internet. Cyberthreats can range from unlawful use of leaked passwords to politically motivated cyberterrorism attacks targeted at infrastructures or sensitive data. Cyberattackers themselves range from amateur actors to state-sponsored groups.
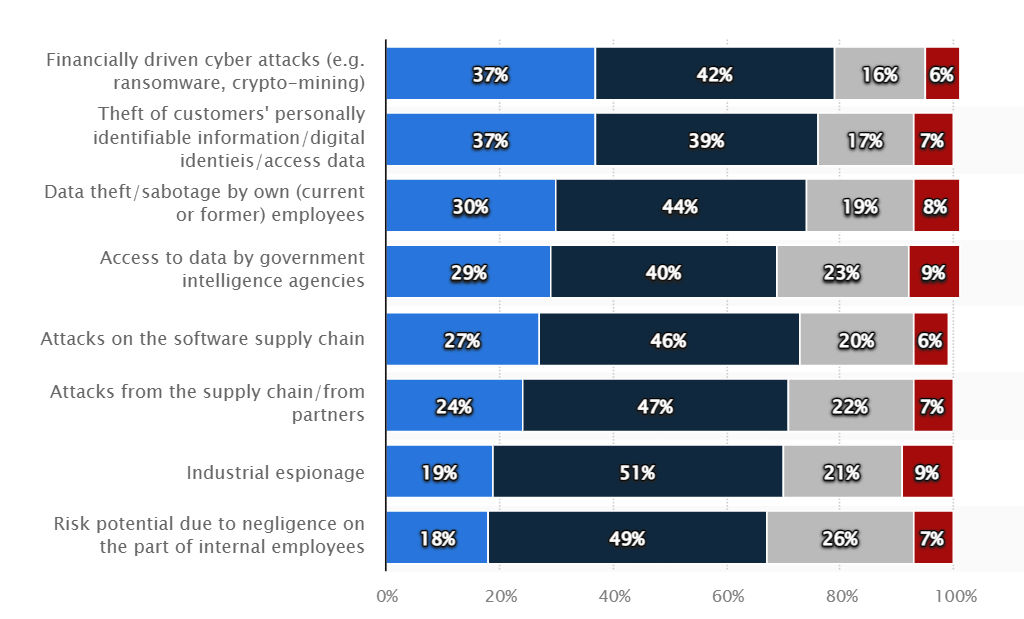
According to Statista’s Cyber attack threat scenarios and potential worst-case impact on businesses worldwide in 2021 report, the most catastrophic cyberthreats for businesses include financially driven cyberattacks, theft of customers’ personally identifiable information and data theft conducted by employees.
Cyber attack threat scenarios and potential worst-case impact on businesses worldwide in 2021 (data by Statista)
Successful cyberattacks can impact businesses small and large on many different levels. Victims of cyberthreats often suffer the following consequences:
- Production line disruptions
- Significant financial losses
- Legal liability problems
- Decline in brand reputation
According to Statista’s Types of cyber crime most frequently reported to the IC3 in 2020 report, phishing, non-payment, extortion, personal data breaches and identity theft were the top cybercrimes in 2020. What is the cost of all this? Cybersecurity Ventures estimates that the cost of cybercrime will grow 15% every year and, consequently, reach $10.5 trillion by 2025.
As reported by AtlasVPN, cybercriminals rake in $1.5 trillion annually. This is three times the annual revenue of Walmart, the world’s biggest retailer. Although cybercrime can be used as a weapon of terrorism, espionage and theft of sensitive intel, it is no secret that most cyberthreats are conducted to make quick money.
Ransomware, for example, allows cybercriminals to blackmail victims into paying ransoms in return for file decryptors. Phishing is another great example of cybercrime, and it often facilitates the theft of credit card information for unauthorized payments or money transfers.
In a recent webinar hosted by IPXO, Zoltan Balazs, Head of Vulnerability Research Lab at CUJO AI, shared that cybersecurity researchers are currently observing a significant increase in scams related to blockchain and cryptocurrency, both of which are trending topics.
To get more insights into cyber threat mitigation from Balazs and other industry leaders, watch the recording of the webinar:
IP address abuse
IP address abuse occurs when internet-connected devices – which is what IP addresses identify – are compromised by malware or cybercrime. For example, if a trojan exploits a device for distributed-denial-of-service (DDoS) attacks, the IP address can be recognized as abusive. What does that mean?
Although the IP holder (e.g., ISP) has no relation to the attacker and has no control over the attack that occurred, they are the ones that need to deal with an IP address that now has a bad IP reputation. IP blocklists catch IPs that relate to malicious activity and tag them as disreputable, which can lead to blocked traffic from that IP address.
IP addresses are also vulnerable to session hijacking and IP address spoofing.
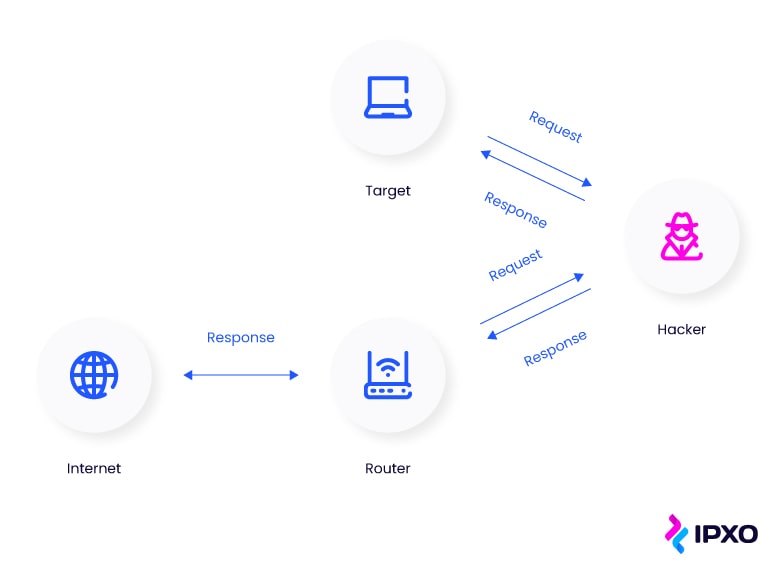
A session is the exchange of information between communicating devices. Session hijacking, or TCP (Transmission Control Protocol) hijacking, occurs when a malicious party hijacks the session ID of one user and takes over their session. What is the purpose of session hijacking? To gain unauthorized access to the information that users are exchanging.
IP address spoofing is a form of session hijacking, but instead of simply trying to take over a session, the hijacker pretends to be a trustworthy party. This is done by creating IP packets with a modified source IP address.
Professional network monitoring, firewalls and packet filtering are crucial cyberthreat mitigation techniques that can help prevent IP spoofing.
DNS hijacking, also known as DNS redirection, is another type of abuse that involves IP addresses. If a hacker successfully hijacks a DNS server, they can divert all traffic to a fake DNS server. Consequently, they can redirect internet users to malicious websites even when they attempt to access legitimate ones.
A good firewall, a DNSSEC system, client locks and strong router passwords are among the mechanisms that can help mitigate DNS hijacking.
In general, the most common types of IP address abuse fall under these categories:
- SPAM – unsolicited mailing
- Malware – bots, attacks, exploits
- Phishing – fraudulent communication via websites and emails
- Copyright infringement – illegal use of intellectual property
- Illegal materials – child sexual abuse, violence, terrorism

Cyberthreat mitigation techniques
If it were not for successful cyberthreat mitigation, we would have a really difficult time surfing the web without facing malware and cyberattacks every step of the way. Fortunately, the architecture of the internet is fortified in a variety of ways. This is what allows us to perform financial operations and communicate safely.
Undeniably, cyberthreat mitigation is crucial. Therefore, cybersecurity experts are working hard to patch all vulnerabilities and fix all security issues as swiftly as possible.
When it comes to IP address security, the most crucial instruments for cyberthreat mitigation include:
- Blocklists
- IP reputation scans
- Know Your Customer (KYC) checks
- Cyberthreat intelligence
Blocklists
You are already familiar with the concept of blocklists, but how exactly do they assist in preventing cyberattacks? Can they be effective against abuse?
First of all, blocklists are not a preventative measure per se. Instead, they denote abuse that has already occurred. When asked about the effectiveness of blocklists during the Cyber Threat Mitigation webinar, Andrius Lapienė, the Staff Security Engineer at IPXO, shared that blocklists should not be used to prevent threats but rather help indicate them so that further mitigation steps could be taken.
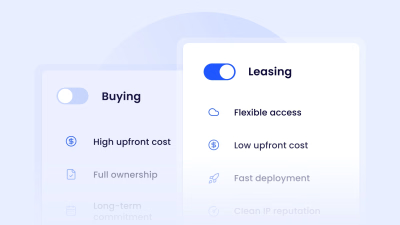
That said, blocklists can help avoid potentially unreliable IP holders. This is particularly important in the businesses of IP leasing and IP brokering. After all, no one wants to spend money on IP addresses that have a poor reputation.
Resource holders who want to lease or sell IP assets must first check if their IP addresses are not registered by known blocklists. There are plenty of free tools online that can assist with that. For example, the MxToolbox Blacklist Check or WhatIsMyIPAddress Blacklist Check.
IP reputation scans
According to Karolis Šimėnas, the DevOps Practice Lead at IPXO, no one who comes to the IPXO platform wants to lease IPs that have a bad reputation and a history of abuse. That’s why IP reputation scanning is one of the most important mechanisms for a high level of IP address abuse observability.
IPXO’s IP reputation scanner scans subnets and checks whether they are valid or invalid. If any of the scanned IPs are blocklisted, the Abuse Prevention team can quickly assess each case and devise a plan on what to do next.
Spamming, copyright infringement, port scanning, and other illicit behavior can bring IP reputation down, and blocklists record all of this activity. “We have 92 blocklists in our database, and we constantly check all those reports,” shared Vincentas Grinius, CEO at IPXO.
Information from reputable blocklists and a trustworthy IP reputation scanner help ensure that disreputable IPs cannot enter the Marketplace. Moreover, this makes it easier to catch abuse incidents quickly.
Know Your Customer checks
Strict KYC policies can help verify customers and minimize the risk of potential IP address abuse. IPXO’s KYC compliance checks ensure that companies interested in leasing IPs via the IPXO Marketplace are trustworthy. This guarantees that IP holders bringing their valuable assets do not need to worry about leasing their IP addresses to parties that might abuse them in various malicious ways.
At IPXO, on average, account verification takes up to 10 minutes. Within this time, three important questions are addressed:
- Does the person registering an account have a link to the company they allegedly represent?
- What services does the registered company provide?
- Are the services provided by the company legitimate?
It is not possible to register an account using a disposable or temporary email address. And it is not possible to create multiple accounts using the same email address.
The most common reasons for account verification rejection include:
- Failure to provide the necessary information
- No connection between the contact and the company
- Lack of social presence and business registration information
- The registered company is considered high-risk
Virgil Truica, DDoS Security Evangelist at Voxility, believes that appropriate KYC practices can help make informed risk assessments and, simultaneously, lower security risks. In a recent IPXO webinar, Truica shared that proper KYC practices helped lower the risk of network security breaches, the number of abuse-related issues and even the number of support tickets at Voxility. This allowed the teams to dedicate their time to other important tasks:
Cyberthreat intelligence
Threat intelligence is the mechanism that enables organizations to understand the threats they face. Cyberthreat intelligence, as the name suggests, revolves around the threats that plague the cyber world. The main purpose of this mechanism is to help identify and prevent various cyberthreats.
With the help of cyberthreat intelligence, organizations can employ historical data to mitigate persistent threats and, consequently, minimize security risks. Although cyberthreat intelligence requires significant investments and relies on continuous innovation, the benefits outweigh the costs.
The main benefits of cyberthreat intelligence:
- Uncovers patterns and threat characteristics
- Speeds up threat prioritization and investigation
- Enables managing high volumes of threats efficiently
- Empowers cybersecurity teams to make informed decisions
- Helps optimize threat mitigation capabilities
- Informs stakeholders about potential risk scenarios
The role of machine learning is exceptionally important in the field of cyberthreat intelligence. It enables cybersecurity experts to understand and predict threats much faster. This can help mitigate threats much more quickly and efficiently.
According to Balazs, machine learning is very useful because it can be used to perform tedious tasks at a very large scale and at a low cost. Balazs believes that with the help of machine learning and AI (artificial intelligence), it is possible to mitigate the global shortage in IT security talent. Therefore, any chance to automate is a big win for any company, especially for companies in the cybersecurity sector.
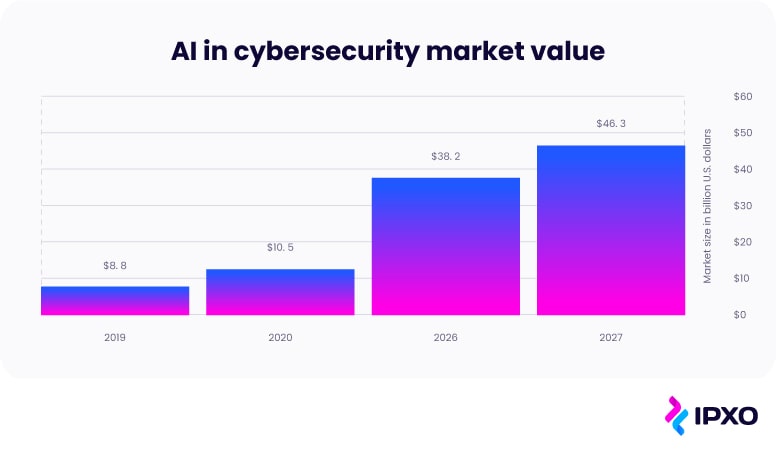
Undeniably, the demand for AI is increasing. Reports show that the market value of AI in cybersecurity will reach $46.3 billion by 2027. A significant increase from just $10.5 billion in 2020.
Prevention is key to successful IP address abuse mitigation
According to Lapienė, there is no ultimate cure for cyberthreats, and the most important task is to balance cyberthreat prevention and mitigation. Lapienė believes that focusing on prevention rather than the so-called cure can even provide the answer to cybersecurity issues:
Lapienė and other guest speakers participating in the webinar unanimously agreed that effective cyberthreat mitigation requires a joint effort from the entire internet community. According to Truica, full transparency from the cyberthreat prevention community benefits both customers and the industry itself.
Truica believes that customers should have access to as much information as possible. That is because transparency can encourage companies to invest more in their cybersecurity and encourage vendors to improve and innovate their cybersecurity products.
The hope within the community is that, in the future, regulatory bodies – such as governments – will join in and help with cyberthreat mitigation and prevention. For now, however, these regulatory bodies are unable to assist.
Professional IP address abuse management: Moving from abuse observability to abuse prevention
The IPXO Abuse Prevention team works around the clock to handle abuse quickly and efficiently. If the team discovers abuse, the IP holder receives a notification indicating that the report is under review.
Different kinds of abuse incidents have different severity levels, which means that while it is possible to resolve some issues quickly, others take time. For example, illegal materials, such as child sexual abuse or terrorism, have the highest priority level and, therefore, are handled the quickest.
To learn more about how IPXO handles abuse, please refer to the Reporting Abuse guide.
Although the measures to successfully deal with abuse incidents are set in place, there is no denying that preventing abuse from happening in the first place is the number one priority.
For this reason, IPXO combines automated abuse reporting, real-time IP address monitoring and the guidance of a dedicated Abuse Prevention team to ensure professional abuse management and a high level of abuse observability.
As you already know, our Abuse Prevention team works with over 90 blocklists, which enables our experts to assess the reputation of every IP address coming into the Marketplace.
Prioritizing cyberthreat and IP address abuse mitigation
While it may be impossible to prevent 100% of all abuse cases, new tools are developed and innovative countermeasures are set in place to ensure that the number of successfully prevented incidents is as close to the golden 100% standard as possible.
IPXO anti-abuse experts work daily to ensure that all IP addresses go back to IP holders clean after the lease period. We aim to ensure that IP holders do not need to be concerned with the reputation of their monetized IP resources. Simultaneously, the preventative measures we introduce create a platform that is safe for IP lessees as well.
As we continue to prioritize both IP abuse mitigation and prevention, we are looking into upgrading the existing mechanisms and implementing new ones to ensure the best possible customer experience.
About the author
Related reading
The hybrid IPv4 strategy: When to lease and when to buy
A practical guide to navigating IPv4 scarcity in 2026. Learn when to lease, when to buy, and how a hybrid IPv4 strategy helps organizations balance cost, flexibility, and long-term…
Read more
IPv4 Buying and Leasing in 2026: A Market Recalibration
The year began with a clear signal: the IPv4 market is adjusting. Find out what's happening and what the market will look like moving on.
Read more
BEAD Network Expansion Will Drive IPv4 Demand – Why Leasing Makes Strategic Sense for ISPs
The Broadband Equity, Access, and Deployment Program represents a $42.45 billion investment in expanding broadband infrastructure across the United States. For many operators, the immediate…
Read moreSubscribe to the IPXO email and don’t miss any news!
